Exciting New Career Paths- The Future of IT Administrators
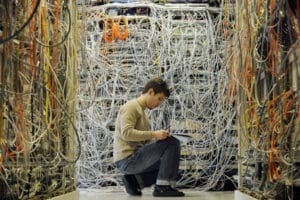
The IT field offers numerous opportunities to the right candidate. You don’t have to stay in the same position for
BY THREAT
BY THREAT
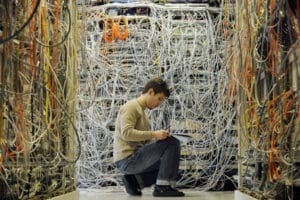
The IT field offers numerous opportunities to the right candidate. You don’t have to stay in the same position for

We always focus on protecting data. The idea of phishing, social engineering, and cyber hacks such as DDoS (distributed denial

A single point of failure (SPOF) is any hardware or software component that could potentially render the entire system unusable

IT is a hot career. Not only are there plenty of people looking for qualified individuals, but there are also

Security awareness is a collaborative effort between security officers, employees, management and executives. Everyone must work together to ensure the

2015 saw some major security breaches unlike previous years. Ashley Madison, Adobe, Experian, CVS and even the IRS were among

We saw some incredible breaches in 2015, where hackers were able to breach several prominent businesses including BlueCross BlueShield, the

Gone are the days that Mac users could avoid malware just by having a Mac. As Mac becomes a popular

Stats indicate that people prefer mobile devices over desktops for accessing the Internet. Phones, tablets and wearable devices are everywhere

2015 saw several prominent hacks that resulted in millions of exposed private data. As attacks become more sophisticated and resilient
Ready to See the Difference?
Discover our advanced security products today.